Here's a look at the Microsoft Log Parser from a different point of view, from the Computer Forensics' side of the house OR Check out a 'Query Analyzer/SSMS' for Log Parser called Log Parser Lizard
SANS - Computer Forensics and Incident Response with Rob Lee - Computer Forensics How-To: Microsoft Log Parser
"As any incident responder will agree, you can never have too many logs. That is, of course, until you have to analyze them! I was recently on an engagement where our team had to review hundreds of gigabytes of logs looking for evidence of hacking activity. I was quickly reminded of how much I love Microsoft Log Parser.
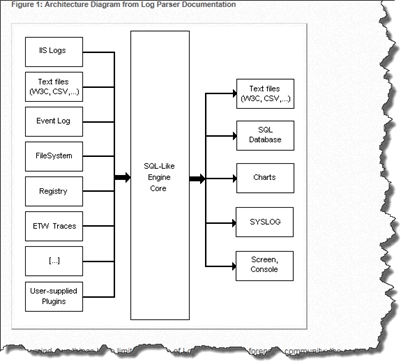
Log Parser is often misunderstood and underestimated. It could possibly be the best forensic analysis tool every devised. Imagine having the ability to take almost any chunk of data and quickly search it using SQL-based grammar. That's Log Parser in a nutshell. It is a lightweight SQL-based search engine that operates on a staggering number of different input types (see Figure 1). Yes, I know that tools like Splunk and Sawmill are built around this same idea, but keep in mind that Log Parser was written in the year 2000. I am constantly amazed at the power it affords the forensic analyst, and you can't beat the price (free). Save perhaps memory analysis, there isn't much it can't accomplish for an incident responder.
...
...
..."
This post provides an different view on using Log Parser. Most posts I've seen are from the IT side of the house, monitoring, logging, etc. This view is from the incident response, computer forensic, side.
It uses a tool I've not seen before, a Query Analyzer/SSMS for Log Parser called Log Parser Lizard. I've been keeping an eye out for Log Parser posts for a while now (my first post about is was in 2004, below...) and I believe this is the fist I've seen Log Parser Lizard. So much to find and learn... :)
Related Past Post XRef:
Log Parser Ping Graph Fun (aka “Using Log Parser to parse command line output”)
SELECT * FROM Log... with the cool tool that’s been around for years, Log Parser!
Download details: Log Parser 2.2
The Unofficial Log Parser Support Site
IIS Diagnostics Toolkit (January 2006)
SQL Server 2000 Report Pack for IIS Logs






No comments:
Post a Comment